Tycoon2FA
Who are Tycoon2FA/Storm-1747?
Tycoon 2FA is a sophisticated Phishing-as-a-Service (PhaaS) platform, while Storm-1747 is the threat actor designation (used by Microsoft and other researchers) for the group that operates it. The group has been active since at least August 2023. The platform is primarily designed to bypass multi-factor authentication (MFA) and steal credentials for enterprise cloud environments, particularly Microsoft 365 and Gmail.
Core Architecture and Mechanics
The platform operates using an Adversary-in-the-Middle (AitM) approach. Unlike traditional phishing kits that simply harvest passwords, Tycoon 2FA functions as a synchronous reverse proxy.
• The Relay: When a victim enters their credentials on a fake login page, the Tycoon server relays those inputs to the legitimate identity provider (like Microsoft) in real-time.
• MFA Interception: Because the session is proxied, the kit can present the victim with legitimate MFA challenges (SMS codes, push notifications, or TOTP tokens) and relay the victim's response back to the genuine service.
• Session Hijacking: Once authentication is successful, Tycoon captures the resulting session cookies. Attackers can then "replay" these cookies to access the victim's account in the future without needing further authentication, even if the user subsequently changes their password.
Advanced Evasion and Evolution
The platform is notable for its continuous technical iteration to stay ahead of security researchers:
- Invisible Unicode Obfuscation: A 2025 version introduced the use of specific Unicode characters (like Hangul Fillers) to encode malicious JavaScript, making it invisible to the human eye and standard text editors.
- DOM Vanishing Act: To evade security scanners, the malicious JavaScript executes in the browser's memory and then deletes its own code from the Document Object Model (DOM), leaving the page structure appearing benign.
- Hybrid Operations: In late 2025, researchers identified a Salty-Tycoon hybrid strain where attacks begin with "Salty2FA" signatures but pivot to the Tycoon 2FA execution chain if the primary infrastructure is compromised, providing "seamless failover" for attackers.
- Persistent OAuth Hijacking: Recent campaigns have shifted toward exploiting persistent OAuth flaws. By proxying legitimate OAuth consent screens for fake enterprise applications, Storm-1747 can obtain refresh tokens that provide long-term, invisible access to cloud resources that survives password rotations and MFA resets.
The Storm-1747 Operator Group
Storm-1747 (also known as the Saad Tycoon Group) manages the infrastructure and sells access to the kit via encrypted channels like Telegram.
• Commercial Model: The kit is sold using a subscription model, typically priced at approximately $120 for 10 days of service.
• Lineage: Researchers believe Tycoon 2FA is an evolutionary descendant of the Dadsec OTT phishing kit, likely created by forking and rebuilding its source code.
• Scale: The group has been highly prolific, with reports indicating involvement in over 64,000 incidents in a single year. In October 2025 alone, Microsoft reported blocking more than 13 million malicious emails linked to the kit.
Similarities with Dadsec
There are significant technical and operational overlaps between Tycoon 2FA and the older Dadsec OTT phishing kit, leading many to conclude that Tycoon 2FA is an evolutionary descendant or a direct clone of the Dadsec platform.
The similarities between these two PhaaS kits include:
- Similar codebase
It's suggested that the developers of Tycoon 2FA likely forked the original source code from the Dadsec OTT kit. This is supported by striking similarities in the core authentication relay logic and the back-end code used to handle the Adversary-in-the-Middle (AiTM) process.
- Identical Administration Panels
The admin panels for both of these bits are described as "almost identical" in design and functionality. Specifically, they share the same layout, buttons, and fonts as well as the following statistical data categories:
- Bots Blocked
- Total Vistits
- Valid Login
- SSO Login
- Invalid Login
- Shared Infrastructure and Delivery Components
- Bypassing MFA and Anti-Bot Tactics
Both kits are built to defeat Multi-Factor Authentication (MFA) by intercepting session cookies and real-time verification codes. Additionally, they employ nearly identical "gatekeeper" strategies to deter security researchers:
- Cloudflare Turnstile: Both use custom HTML pages to embed Cloudflare Turnstile challenges to filter out automated scanning tools.
- Thematic Deception: Earlier versions of Tycoon 2FA even repurposed the specific text used by Dadsec on these challenge pages, stating: "While we are checking your browser..."
URL Patterns
Based on the research that we have carried out in identifying Tycoon2FA infrastructure, we were able to collate a list of URLs and pull out the common patterns used.
Subdomain Impersonation (Tech & Service Lures)
The most prominent pattern is the use of subdomains that mimic legitimate technical services, enterprise tools, or security features to gain trust. These include:
• Security/Authentication: 2fa, mfa, sso, verify, adblock, captcha, security, encryption, vault, and authy.
• Cloud & Infrastructure: azure, aws, cloudops, k8s, kubernetes, docker, gateway, loadbalancer, route53, serverless, and cdn.
• Enterprise & Productivity Tools: sharepoint, onedrive, exchange, teams, outlook, trello, asana, slack, zoom, zendesk, confluence, bitbucket, and github.
• Development Frameworks: react, angular, vue, flutter, python, php, nodejs, typescript, graphql, and prisma.
• Document/File Sharing: docs, pdf, drive, dropbox, file, viewer, and signature-document-control.
Path and Suffix Structure
The Alphanumeric Hash: After the domain, there is usually a path containing a seemingly random alphanumeric string, often interspersed with special characters like @ or ! (e.g., /NjIwYLL9BpQ6dzzHX!330k/ or /H18PEHm@UhGuVVtzLB/).
• Victim Identification Suffix: A very consistent pattern is the inclusion of the victim’s email address at the end of the URL, prefixed by specific symbols:
◦ /$ Prefix: By far the most common, followed by the plain-text email address (e.g., .../$user@example.com).
◦ /* Prefix: Used in several instances (e.g., .../*user@example.com).
• Encoded Emails: In many cases, the email address is Base64 encoded instead of being in plain text, appearing as a string ending in = or == (e.g., /$cmFoYW1pbHRvbkBlcXVpbml4LmNvbQ==/).
Domain and TLD Trends
The domains used often appear to be procedurally generated or registered through cheap TLDs to facilitate rapid infrastructure rotation:
• Suspicious TLDs: Frequent use of .ru, .sa.com, .biz.id, .in.net, .za.com, .live, .click, .icu, and .solutions.
• Pseudo-Random Domain Names: The main domain often consists of nonsensical or concatenated words like gousoolaishi, thiwoolea, Northernbliss, craidaiyio, and wizzly.
• Chailafu Pattern: A recurring pattern involves subdomains on the chailafu.ru domain, often using a hyphenated prefix (e.g., shadeon-he1osmokex.chailafu[.]ru or sky-z1mmaskon.chailafu[.]ru.
Phishing Email and CAPTCHA Page
Email Example
Below shows two screenshots of emails we have recently seen targeting customers with Tycoon2FA phishing kits.
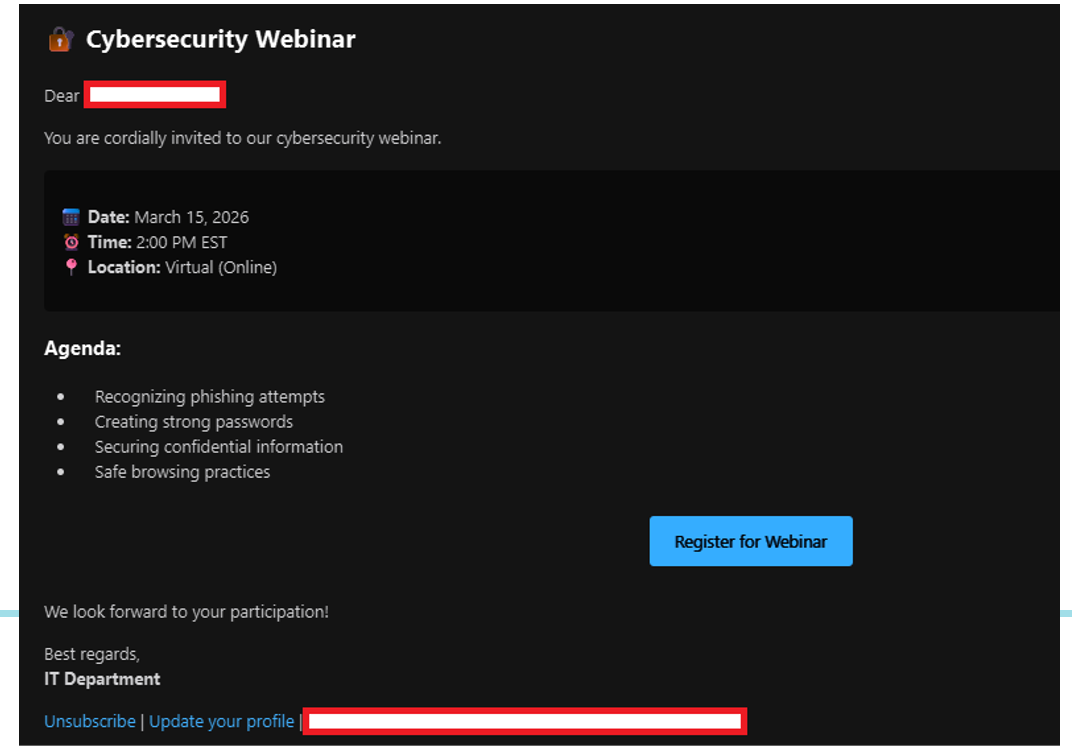
Figure 1 - Email example with the subject containing "Secure Your Skills: Join Our Cybersecurity Webinar!" containing a Tycoon2FA phishing link
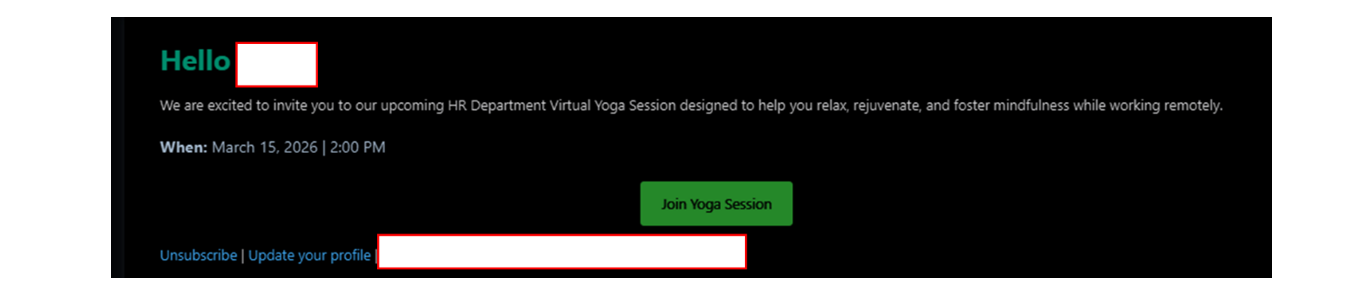
Figure 2 - Email example with the subject containing "unwind with us at the HR Virtual Yoga Session!" containing a Tycoon2FA phishing link
HTML Content
Based on the tracking of these phishing kit pages, we have managed to identify five new pre-verification CAPTCHA pages being used throughout December/January.
After reviewing the five distinct HTML patterns used by Tycoon2FA (Storm-1747) as "gatekeeper" or CAPTCHA pages. These pages serve a dual purpose: they filter out automated security scanners that might flag the phishing site, and they "condition" the victim to perform a simple security-related task before they are redirected to the actual credential harvesting page.
Shield Glow CAPTCHA
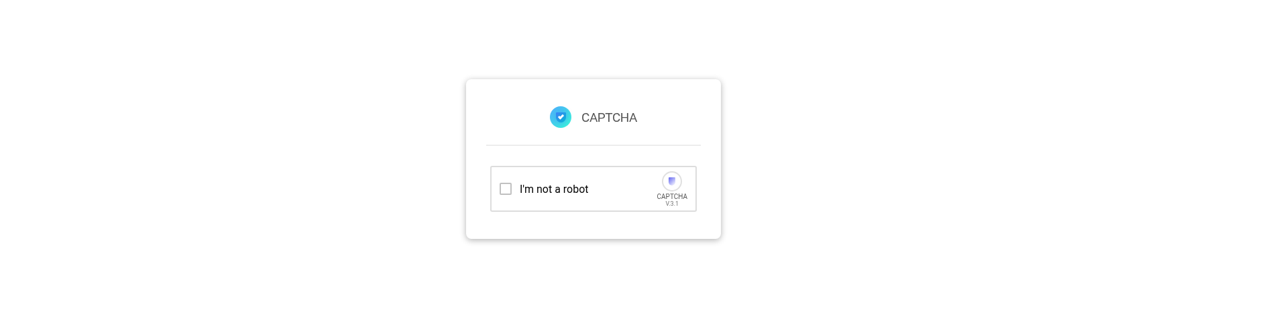
Figure 3 - Screenshot showing example of the Shield Glow CAPTCHA Page
Key HTML Elements:
- <title>CAPTCHA</title> I'm not a robot, V.3.1
Analysis:
This variant is designed to leverage brand familiarity. It directly mimics the visual language of common security tools like Google’s reCAPTCHA. The inclusion of a version number (V.3.1) is a technical detail intended to lend an air of legitimacy to the page.
Green ENABLED CAPTCHA
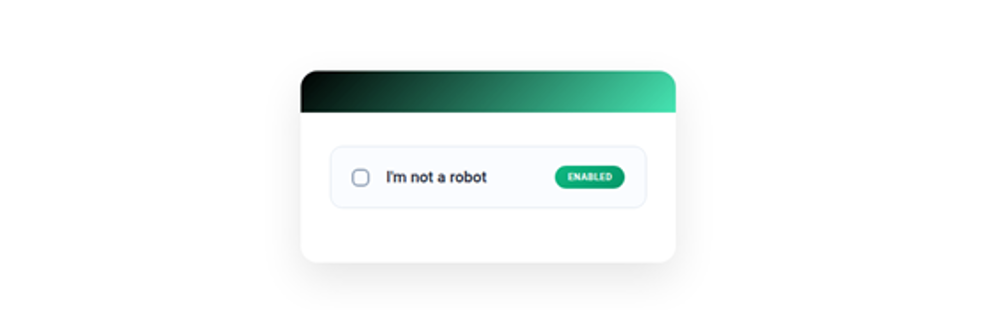
Figure 4 - Screenshot showing example of the Green ENABLED CAPTCHA Page
Key HTML Elements:
- I'm not a robot
- ENABLED
- Verifying your request...
Analysis:
- Unlike the "Shield Glow" which mimics a process, this variant focuses on a state of completion. The use of the word "ENABLED" suggests that the security check has already been triggered or passed, urging the user to click and proceed to the next step of the lure.
Circle Glow CAPTCHA
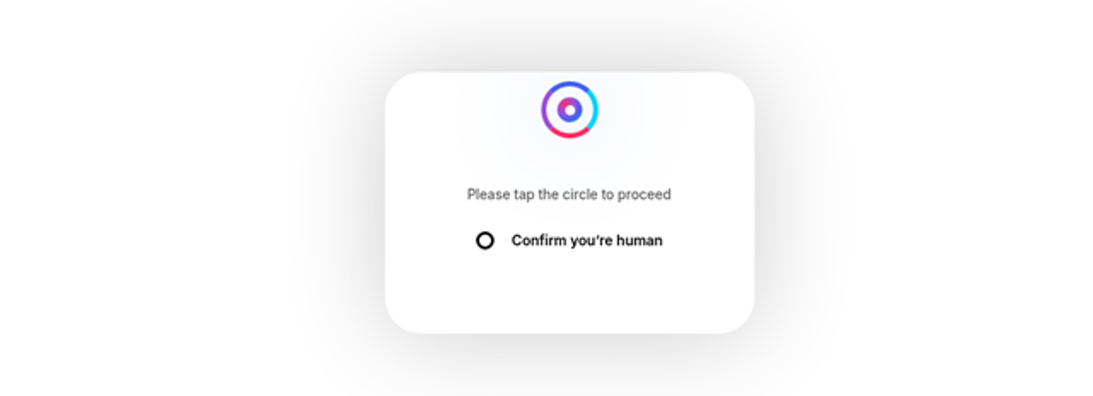
Figure 5 - Screenshot showing example of the Circle Glow CAPTCHA Page
Key HTML Elements:
- Please tap the circle to proceed
- Confirm you're human
- Human check required
Analysis:
This is a more interactive page. Rather than a standard checkbox, it requires specific physical action: tapping a circle. This is specifically designed to defeat automated bots that can click standard buttons but might struggle with identifying and interacting with specific shapes within a custom-rendered DOM.
Security Check CAPTCHA
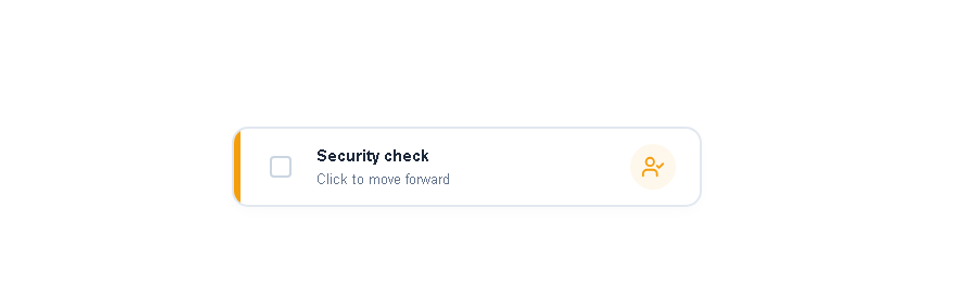
Figure 6 - Screenshot showing example of the Security Check CAPTCHA Page
Key HTML Elements:
- Bot activity detected. Reloading...
- Human check required
Analysis:
This version uses a formal, technical tone. It avoids the brand-mimicry of the others and instead presents a mandatory system requirement. This style is often seen in corporate environments, making it highly effective for B2B phishing campaigns.
Text Entry CAPTCHA
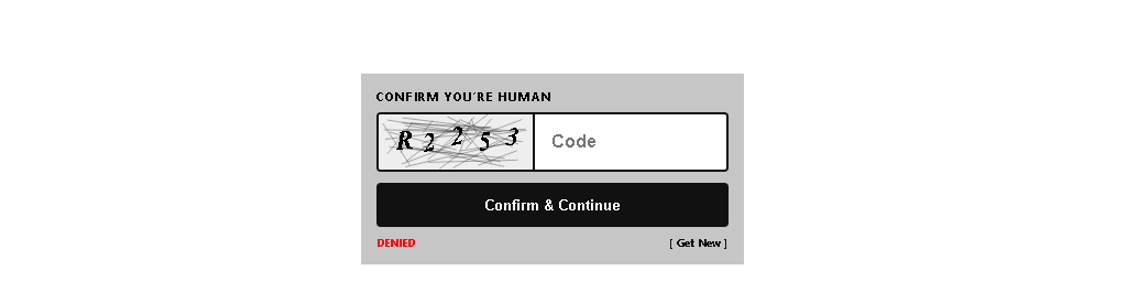
Figure 7 - Screenshot showing example of the Text Entry CAPTCHA Page
Key HTML Elements:
- Enter displayed text:
- <div class="re-text">CAPTCHA</div>
- checkCaptcha()
Analysis:
This CAPTCHA page is different from the others that we have seen. The attackers seem to have shifted away from the usual "Click Here to Verify" to a more complex CAPTCHA where they are asking the user to confirm they are human by entering the text they see on screen. The HTML suggests that the CAPTCHA is random as it shows elements of other CAPTCHA verification options such as "Select all Images".
Change in Captcha Pages
The evolution of Tycoon2FA (Storm-1747) shows a clear trajectory: the platform has moved from simple visual mimicry to sophisticated, multi-layered technical evasion designed to defeat both human intuition and automated security scanners.
The earlier variants from December 2025 focused heavily on psychological familiarity and interactive challenges to filter out simple bots:
• Mimicry (The Shield Glow): Initially, the kit leaned on the visual trust of established security tools, using phrases like "I'm not a robot" and "V.3.1" to mimic Google’s reCAPTCHA.
• Interactive Complexity (The Circle CAPTCHA): To stay ahead of more advanced automated crawlers that can handle simple checkboxes, the group introduced specific physical tasks, such as "tap the circle to proceed". This forces a more complex human-like interaction that many headless browsers used by security firms might not execute correctly.
• Status-Based Urgency (GreenCaptcha): The "ENABLED" status variant was used to create a seamless transition for the victim, making the security check feel like a completed prerequisite rather than an obstacle.
By January and February 2026, the tactics shifted toward corporate/professional branding:
• Policy Mimicry (Security Check): The "Human check required" variant moved away from tool-mimicry and toward impersonating a standard corporate security policy. This is more effective for B2B phishing because it aligns with what employees expect when accessing internal resources like SharePoint.
• Minimalist Obfuscation (Text Entry): The most recent "TextEntry" variant shows a shift toward a very minimalist HTML structure. This minimalism is a defensive tactic; by reducing the "footprint" of the page, there is less code for signature-based security scanners to flag.
Microsoft View
Stats
The December 2025 report from Microsoft provides a detailed statistical breakdown of the phishing landscape, specifically highlighting the continued influence of Tycoon2FA (Storm-1747) despite a general seasonal dip in volume. Microsoft Defender for Office 365 detected over 2.1 billion email-based phishing threats, a 9% decrease from November.
Delivery Vectors:
◦ Link-based attacks: 77% (up from 68% in November).
◦ Payload-based attacks: 14% (down from 15%).
◦ Text-only attacks: 9% (down from 17%)
BEC Attacks: Business Email Compromise (BEC) attacks decreased by 22% to 2.86 million, with 81% of these being generic outreach (e.g., "Are you at your desk?")
Tycoon2FA (Storm-1747) Specific Stats
• Email Volume: Microsoft detected more than 13.4 million malicious emails associated with Tycoon2FA, a sharp 43% decrease compared to November.
• Infrastructure Dominance: Nearly half of all Tycoon2FA domains were hosted on five specific TLDs/SLDs: .SA.COM (20%), .RU (11%), .IN.NET (9%), .COM (8%), and .RU.COM (4%).
• MFA Bypass Influence: Despite its drop in volume, the group drove more than three-quarters (76%) of all CAPTCHA-gated phishing attacks, an increase from 53% in November.
• Tactical Shifts: The volume of malicious SVG payloads decreased by 36% in December; Microsoft attributes the overall decline of SVG use in the threat landscape primarily to Tycoon2FA moving away from this file type for its CAPTCHA attacks.
Notable High-Volume Campaigns
• 4th December (Docusign Theme): A massive Tycoon2FA campaign sent over 623,000 confirmed messages to approximately 152,000 organisations across 156 countries. It used more than 300 likely-compromised domains to deliver CAPTCHA-gated links.
• 30th December (HTML-based): A late-month spike involving over one million malicious.
Bridewell View
Based on the analysis of the roughly 3300 email log records provided in our sources, here is the detailed breakdown of the Tycoon2FA (Storm-1747) infrastructure, delivery success, and numerical activity timelines spanning from October to March.
Domains, TLDs, Delivery Success, Infrastructure Hosting, Stats, Dashboard
The data sample reveals clear statistical trends regarding how different attack infrastructures fare against email security gateways. While the vast majority of volume is caught, a significant raw number of malicious emails still bypass filters:
- Total Email Records Analysed: ~3300
- Blocked / Quarantined: ~2892 records (~88%). The high-volume, rapid-fire campaigns are largely intercepted.
- Delivered (Inbox / On-Premises): ~299 records (~9%). This highlights a severe threat, as nearly a quarter of the malicious emails bypassed filters.
- Junked / Deleted Items: ~84 records (~2.5%). These are typically mid-tier campaigns caught by secondary heuristics.
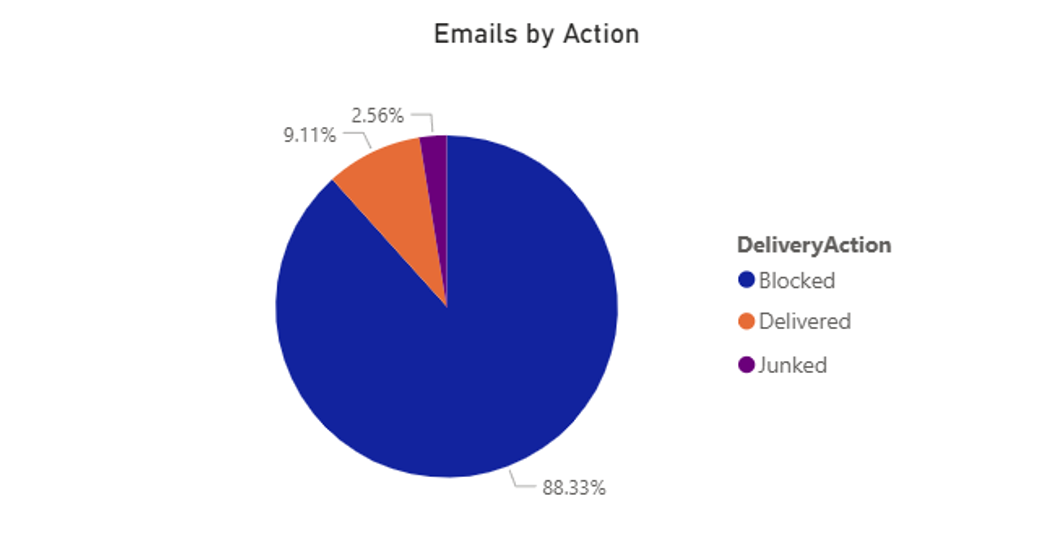
Figure 8 - Image showing the amount of emails Blocked, Delivered or Junked
The threat actor uses a dual strategy: deploying massive volumes of cheap domains while simultaneously abusing trusted SaaS platforms to guarantee delivery.
Top 5 Malicious TLDs (By Volume):
- .za.com: ~1200+ records (Highest raw volume)
- .com.ru: ~1100+ records
- .sa.com: ~300+ records
- .biz.id: ~50+ records
Storm-1747 heavily utilises subdomains that impersonate IT, developer, and cloud environments to trick security scanners. The logs show heavy use of:
- Developer/Tech: terraform, perl, sass, brotli, kali, playwright, nginx, elixir, appsmith.
- Cloud/Network: layout, balance, opacity, uptime, gateway, proxy.
- File/System: formid, region, local, closed, ux, disk, build.
The adversary constantly rotated through prefixes to evade standard static signature blocks. Naming conventions were chosen to mimic legitimate file-sharing or corporate infrastructure:
- country[.]thutregou[.]za[.]com
- build[.]thutregou[.]za[.]com
- disk[.]thutregou[.]za[.]com
- token[.]thutregou[.]za[.]com
- closure[.]thutregou[.]za[.]com
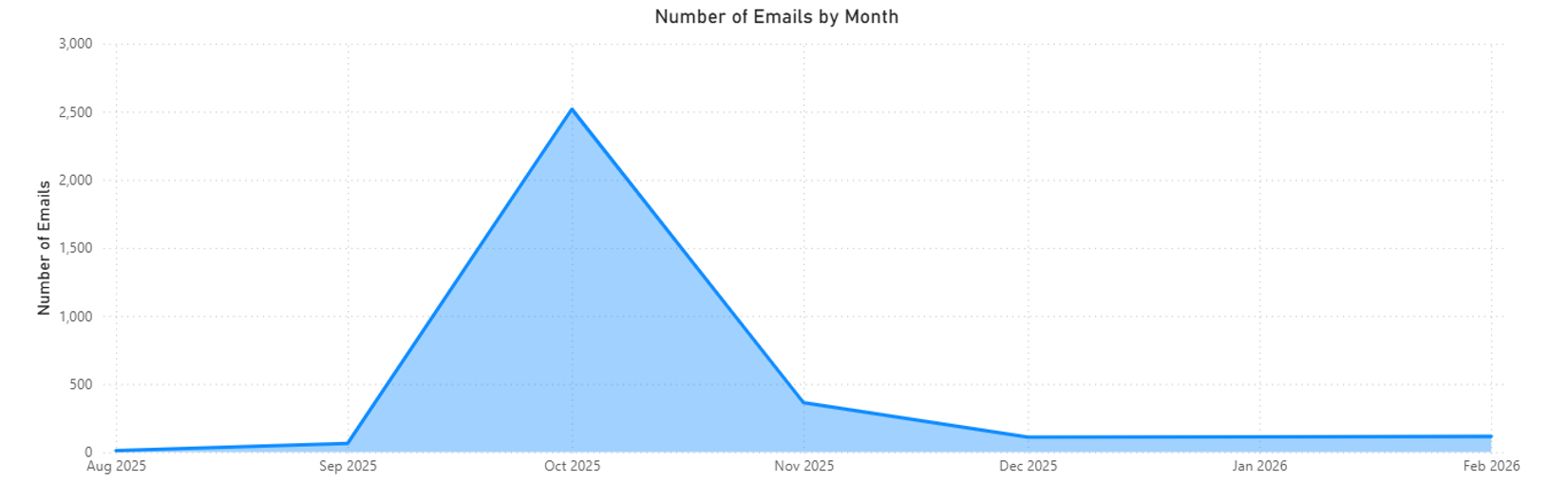
Figure 9 - Graph showing the volume of emails per month
Activity Timeline - Oct - Nov
This period was defined by massive, high-velocity "spray and pray" blasts using procedurally generated subdomains.
- October 10 (The .za.com Blitz): A massive wave of ~1200 logged emails hit targets using thutregou.za.com (leveraging subdomains like disk, token, build, closure, and country). Over 95% of these were successfully blocked/quarantined.
- October 14 (The .com.ru Blitz): The largest single burst in the data deployed ~1100+ logged emails using hioweawou.com.ru (ux, local, region, closed, formid). This was highly ineffective, resulting in a ~98% blocked rate.
- Early/Mid-November: Activity shifted to .sa.com and .solutions. Campaigns using shaimarea.sa.com (subdomains: tokenizer, verifymsg) generated ~20 records, which were highly evasive and largely marked as Delivered to inboxes. A campaign on hejidoo.solutions (~30 records) was mostly junked or blocked.
- November 14 (The "Refresh" Campaign): An attack using refresh.faimihoo.sa.com sent ~15 emails. This was highly effective, with nearly 75% delivered to user inboxes.
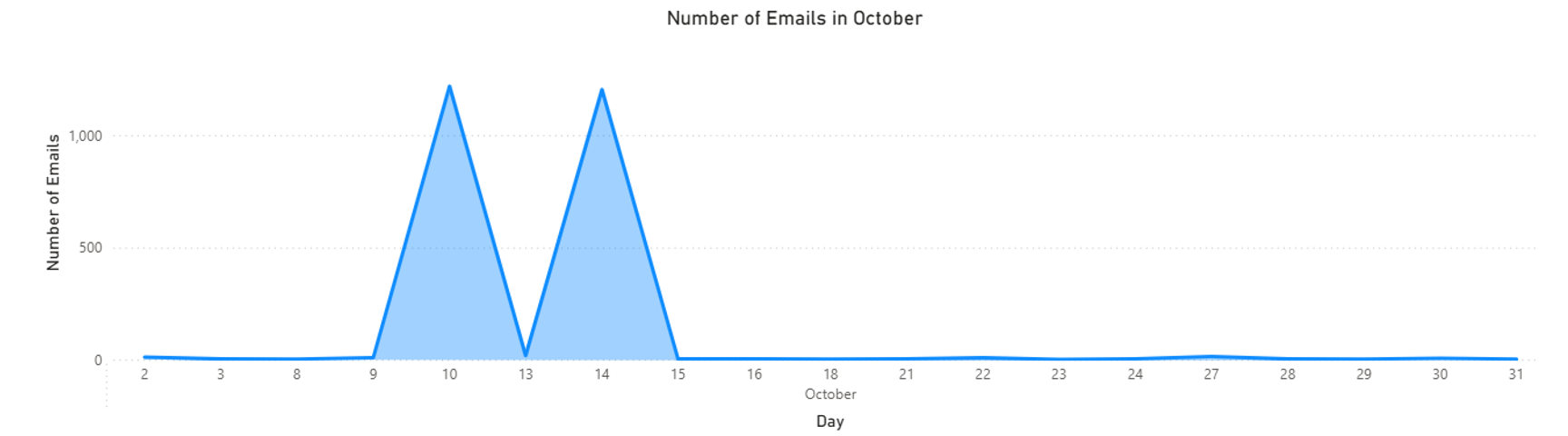
Figure 10 - Graph showing the number of emails throughout October
Activity Timeline - Nov - Dec
During this period, raw volume decreased, but the actor deployed highly specific lures.
- Late Nov / Early Dec: Campaigns pivoted to .in.net and .biz.pl (jeayacrai.in.net, fuwestea.biz.pl). The ~15 records observed here were almost entirely blocked.
- Mid-December (Dec 15-22): The actor utilised .click and .in.net domains, specifically thiociofrou.click (subdomains: tracing, traffic, clone) and piogooye.in.net. These successfully bypassed gateways and were mostly delivered to inboxes.
- Late December: Smaller, sporadic campaigns used domains like drafrouja.sa.com and thoushe.my.id (~10 records), which were entirely blocked.
Activity Timeline - Dec – Jan
The new year saw a rotation to business-oriented TLDs.
- Early January (Jan 4-8): The group spun up roughly ~30 records on .co, .business, and .biz.id TLDs (cache.thucalea.co, proxy.choroosha.business, io.redruthou.biz.id). Security filters caught up quickly, resulting in a 100% blocked rate.
- Mid-January (Jan 8-12): A smaller campaign using pwa.cheajudre.help (~6 records) proved highly evasive, with the majority marked as delivered.
- Late January (Jan 22-23): A massive volume spike returned, pushing over ~30 records through kali.yioyeamou.biz.id. These blasts were rapidly detected and 100% quarantined.
Activity Timeline - Jan – Feb
February demonstrated technical evolution, with the introduction of Domain Generation Algorithms (DGA) and targeted document lures.
- Early February (Feb 2): A small burst (~8 records) on bubble.fibivi.com was successfully blocked.
- Mid-February (Feb 20-21) - DGA Tactics: The actor abandoned readable tech words and deployed procedurally generated, random alphanumeric subdomains on criocrooha.digital (e.g., a7e6zi2k54, zr9w2q3eum, ktnfokyo3l). Despite this obfuscation attempt, all ~30 records were blocked.
- Late February (Feb 25) - Document Lures: Concurrently, the group deployed highly tailored document lures hosted on .ink and .biz.id (e.g., lpdlectricalwholesalersdocx.hoodiomou.ink, scottishdenturedocx.hoodiomou.ink, neossgroupdocx.neakoothu.biz.id). These ~10 records were highly successful, achieving a near 100% Delivered rate to user inboxes.
- Late February (Feb 27): A high-volume burst returned using developer subdomains on kokejo.digital (billing, playwright) generating ~15 records, all of which were blocked.
Tycoon2FA Takedown
Just as the scale and sophistication of Tycoon 2FA seemed to be peaking, the threat landscape experienced a massive shift this week. A coordinated international law enforcement operation—led by Europol and Microsoft, and supported by industry partners including TrendAI™, Cloudflare, and Proofpoint—successfully dismantled the Tycoon 2FA infrastructure.

Figure 11 - Domain Seizure warning displayed on Tycoon2FA Infrastructure
Source: TrendMicro
The scale of the disrupted operation is staggering. According to TrendAI researchers, who provided actionable intelligence and infrastructure mapping for the takedown, Tycoon 2FA had amassed approximately 2,000 criminal users and spun up over 24,000 domains since its inception in August 2023. The joint operation seized over 300 active domains and identified operators operating under monikers like "SaaadFridi" and "Mr_Xaad".
A 30-Day Telemetry Drop
We don't just have to take the press releases at face value; the impact of this disruption is immediately visible in our own email telemetry from the past 30 days.
Looking at the late-February logs, Tycoon 2FA was operating at maximum velocity. We observed massive, automated bursts of emails utilising procedurally generated domains. However, as we move into March and the takedown operation initiated, the Tycoon 2FA infrastructure completely flatlines. Following a final localised burst of "Invitation to collaborate" lures on March 7, the volume drops off a cliff. By March 8, 9, and 10, our logs show only a mere trickle—single, isolated emails being caught by the quarantine.
Residual Infrastructure
While the massive volume drops are highly encouraging, our investigation of the remaining March telemetry reveals a sobering reality: some of the Tycoon 2FA phishing CAPTCHA pages are still live.
Despite the primary disruption, our logs from March 7 through March 10 show a lingering trickle of highly isolated attacks—such as a "Invitation to collaborate rsvp" lure hosted on .insure and a "SPECIAL INVITE" lure hosted on .za.com. When investigating these residual URLs, the familiar Tycoon 2FA "gatekeeper" CAPTCHA pages still render and function.
There are several reasons for this lingering activity, aligning with warnings from TrendAI researchers involved in the takedown:
- Decentralised Infrastructure: PhaaS platforms operate on a sprawling web of compromised third-party sites, legitimate SaaS platforms, and thousands of disposable domains. While the central Command and Control (C2) servers and proxy relays were seized, some of the peripheral domains and localised HTML payloads remain active on the web until their respective hosting providers independently purge them.
- Affiliate Adaptation: As TrendAI notes, taking down the core platform is not the absolute end of the work. Operators and affiliates are highly agile and will attempt to rebuild, migrate to new infrastructure, or pivot to competing PhaaS platforms. The live CAPTCHA pages we are seeing may belong to surviving criminal affiliates attempting to keep their individual campaigns breathing on secondary proxy networks.
- Persistent Danger: A live CAPTCHA page means the threat to the end-user is still very real. Furthermore, any session cookies or credentials harvested prior to the seizure remain in circulation and are actively being monetised by access brokers.
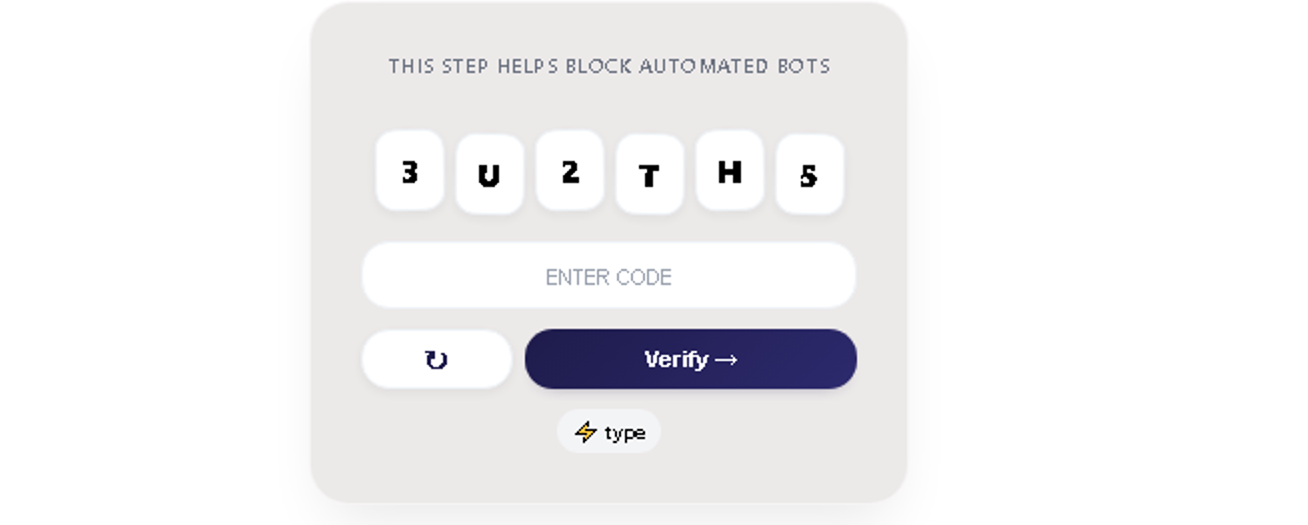
Figure 12 - Screenshot showing the CAPTCHA page hosted on the "Invitation to collaborate rsvp" campaign
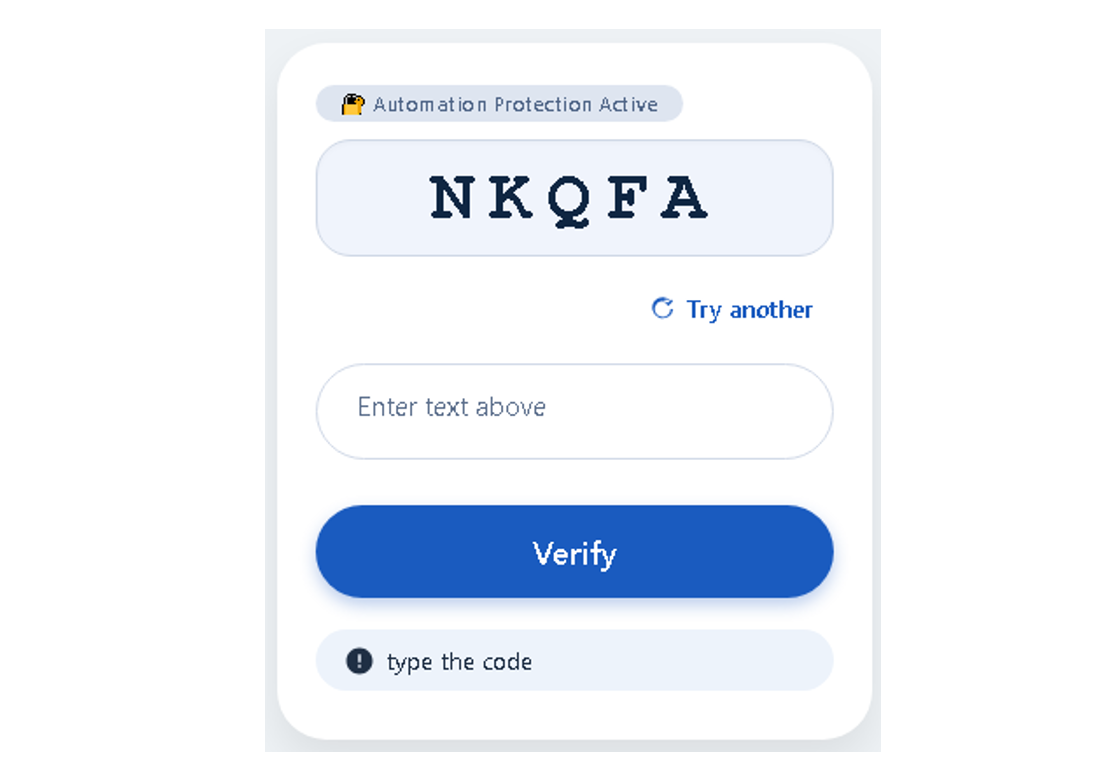
Figure 13 - Screenshot showing the CAPTCHA page hosted on the "SPECIAL INVITE" campaign
Conclusion
Tycoon 2FA (operated by Storm-1747) represented a critical escalation in the modern phishing threat landscape. Up until its recent disruption, it stood as a highly agile, continuously evolving platform that successfully industrialised Multi-Factor Authentication (MFA) bypass through its Adversary-in-the-Middle (AiTM) architecture.
While our analysis of over 3,300 email records shows that email security gateways successfully intercepted the vast majority (~88%) of high-volume, "spray and pray" blasts using disposable TLDs (like .com.ru and .za.com), this volume acted as a smokescreen. The true danger lay in the ~9% of malicious emails that successfully bypassed filters and reached user inboxes. By tactically abusing trusted SaaS platforms, employing dynamic CAPTCHA-gating to deter security scanners, and utilising targeted document lures (such as .ink domains), Storm-1747 ensured a consistent delivery of high-quality, evasive lures to enterprise targets.
However, the threat landscape experienced a massive shift in early March 2026 when a coordinated international law enforcement operation—led by Europol and Microsoft, and supported by a massive coalition of industry partners including TrendAI™—successfully dismantled the Tycoon 2FA infrastructure. By seizing over 300 active domains, this coalition disrupted an operation that had amassed approximately 2,000 criminal users and spun up over 24,000 domains since August 2023. TrendAI researchers even identified the platform's likely developers operating under the monikers "SaaadFridi" and "Mr_Xaad".
Despite this monumental victory, the continuous technical iteration of the kit prior to its takedown highlights broader, structural issues within the Phishing-as-a-Service (PhaaS) ecosystem that will undoubtedly outlive Tycoon 2FA:
- Democratisation of Advanced Attacks: By offering a subscription-based model, sophisticated AiTM capabilities became accessible to low-skill threat actors who simply purchased a turnkey solution.
- Commercial Maturity and Redundancy: The PhaaS landscape operates increasingly like the legitimate SaaS industry. The introduction of "hybrid operations" demonstrates a focus on service reliability. Even with Tycoon 2FA offline, attackers will quickly pivot to surviving frameworks.
- The Shift from Passwords to Session Tokens: PhaaS kits are driving a fundamental shift in attacker objectives. By stealing refresh tokens, attackers gain long-term, invisible access to cloud resources. Crucially, taking down the platform does not undo the damage: stolen session cookies and credentials harvested prior to the seizure remain in circulation and are actively being leveraged by access brokers.
- Persistent Evasion and Residual Threats: Modern PhaaS platforms are defined by their anti-analysis features, such as CAPTCHA challenges. As our own 30-day telemetry proves, the fact that some of these Tycoon 2FA CAPTCHA pages remain live and functional today is a stark reminder of this resilience. Criminal affiliates are highly agile and will attempt to keep their individual campaigns breathing on secondary proxy networks that have not yet been purged.
The dismantling of Tycoon 2FA is a massive win for cross-industry collaboration, but it is a battle won, not the war. The presence of live, residual infrastructure in our latest logs proves that the threat is still twitching. The temporary vacuum left by this operation provides organisations with a critical window of opportunity. To combat the mature PhaaS landscape, defensive strategies must shift from reactive blocklisting to proactive, identity-centric security. Defeating the inevitable successors to Tycoon 2FA will require the widespread adoption of phishing-resistant authentication (such as FIDO2 security keys or passkeys), aggressive conditional access policies, and continuous Identity Security Posture Management (ISPM) focused on anomalous session token usage rather than just initial login attempts.
References
- https://digitalcommons.odu.edu/cgi/viewcontent.cgi?article=1132&context=covacci-undergraduateresearch
- https://exchange.xforce.ibmcloud.com/osint/guid:7d64186c9d4845e38c8534ae0c56037c
- https://flare.io/learn/resources/phishing-kits-economy-cybercrime
- https://freemindtronic.com/persistent-oauth-flaw-tycoon-2fa-en/
- https://hipaatimes.com/tycoon-2fa-phishing-kit-bypasses-mfa-protections-on-microsoft-365-and-gmail
- https://www.cisecurity.org/insights/blog/ms-isac-member-reported-phishing-likely-from-tycoon2fa-phaas
- https://www.csoonline.com/article/4100393/hybrid-2fa-phishing-kits-are-making-attacks-harder-to-detect.html
- https://www.cybereason.com/blog/tycoon-phishing-kit-analysis
- https://cyberfraudcentre.com/unveiling-tycoon-the-emergence-of-phishing-as-a-service-systems
- https://www.dnsfilter.com/blog/tycoon-2fa-infrastructure-expansion
- https://www.darktrace.com/blog/mfa-under-attack-aitm-phishing-kits-abusing-legitimate-services
- https://blog.barracuda.com/2025/01/22/threat-spotlight-tycoon-2fa-phishing-kit
- https://blog.knowbe4.com/tycoon-2fa-phishing-kit-grows-more-sophisticated
- https://blog.sekoia.io/tycoon-2fa-an-in-depth-analysis-of-the-latest-version-of-the-aitm-phishing-kit/
- https://levelblue.com/blogs/spiderlabs-blog/phaas-the-secrets-the-hidden-ties-between-tycoon2fa-and-dadsecs-operations
- https://www.levelblue.com/blogs/spiderlabs-blog/tycoon2fa-new-evasion-technique-for-2025
- https://www.microsoft.com/en-us/security/blog/2026/01/06/phishing-actors-exploit-complex-routing-and-misconfigurations-to-spoof-domains/
- https://www.proofpoint.com/us/blog/email-and-cloud-threats/aitm-phishing-attacks-evolving-threat-microsoft-365
- https://www.proofpoint.com/us/blog/email-and-cloud-threats/tycoon-2fa-phishing-kit-mfa-bypass
- https://www.proofpoint.com/us/blog/threat-insight/microsoft-oauth-app-impersonation-campaign-leads-mfa-phishing
- https://spycloud.com/blog/an-analysis-of-credentials-phished-by-tycoon-2fa/
- https://www.spamtitan.com/blog/tycoon-2fa-phishing-kit-bypasses-mfa/
- https://www.scworld.com/news/tycoon-2fa-phishing-kit-update-timeline-reveals-new-evasion-techniques
- https://socradar.io/blog/tycoon-2fa-an-evolving-phishing-kit-phaas-threats/
- https://teckpath.com/tycoon-2fa-shifted-threat-landscape-2025/
- https://thehackernews.com/2025/12/new-advanced-phishing-kits-use-ai-and.html
- https://thehackernews.com/2026/01/microsoft-warns-misconfigured-email.html
- https://www.paubox.com/news/phishing-kit-that-bypasses-mfa-targets-gmail-and-microsoft-365
- https://www.sekoia.io/en/glossary/tycoon-2fa-phishing/
- https://www.trendmicro.com/en_us/research/26/c/tycoon2fa-takedown.html
- Microsoft Defender Threat Intelligence