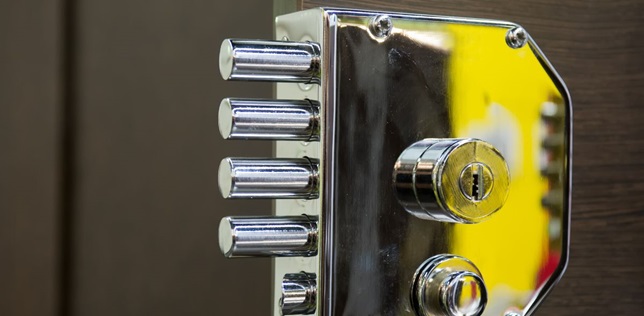
You may not know this, but many people who practice computer hacking (either in their spare time, as a job or as a malicious hacker) also have another passion. You see, breaking into a computer system is an art requiring talent, patience, knowledge and a lot of luck. While most of the probing and testing develops utilising tools and coding, the process is essentially the digital equivalent of picking a lock. Lock picking is a physical manifestation of what they try to accomplish in the digital world, so it’s no surprise that most hackers are also expert lock pickers. But what attracts people to this skill set, and how can it be used for good, and for evil?
What Do Lock Picking and Hacking Have in Common?
In many ways, physical lock picking really gets to the heart of what it means to be a computer hacker in almost every sense. Essentially, the practice of successfully picking a lock in the real-world, mimics what hackers do in the virtual world. They work to find vulnerabilities and flaws in systems, with the ultimate goal of unlocking the secrets inside and, as with lock picking, the motivations can be different. For example, a burglar would pick a lock to get inside and steal from the owner, in the same way a cyber criminal would hack a system to steal the data inside. But a locksmith might pick that same lock to let the owner back inside the house, or to show that the lock isn’t secure enough so a new one can be bought, just like a white hat hacker would break into a system to reveal and patch its flaws. For both sides, the appeal is the same; it’s about solving problems, finding flaws and understanding how complex systems work. Really, it’s no wonder computer enthusiasts gravitate towards lock picking.
The Dark Side of Hacking
Of course, hacking has its dark sides. We hear about these all the time. Individuals or gangs of cyber criminals, who utilise expert hackers looking for ways to break into our systems and steal our money and our data. The appeal of the ‘dark side’ of hacking is quite simple really – it’s usually money, information or power. But cyber criminals don’t always spend their time hunched over keyboards trying to crack the code, they also spend a lot of time developing scams designed to give them easy access into a system. These are what’s known as ‘black hat hackers’, and they are the equivalent of burglars and criminals looking for physical premises – whether business or residential – to target. Sometimes the targets are planned, sometimes they’re random, but either way, the goal is the same – and it’s malicious.
Come to the Light Side
On the other side of things, we have ‘white hat hackers’, otherwise known as the good guys. The security researchers, who spend their time hacking to find vulnerabilities, and then inform enterprises and web developers of the changes that need to be made. But white hat hackers are driven by the same curiosities as black hat hackers. They still want to understand the puzzle, know how all the pieces fit together and find the flaws that let them crack the system. They still enjoy the rush that goes with a successful hack or breaking through security protocols and achieving their goal. The difference is, they don’t want to do anything malicious with it. Instead, they use what they’ve learnt to improve the systems, and relish a tougher challenge next time. The white hack hackers are the locksmiths of the cyber world, the members of the master locksmith’s association, the people who do it for the joy of doing it, and to improve the security of others.
For more information read the Understanding Black, White and Red Hat Hackers article.