What is the NIS Directive?
The NIS Directive is an EU-wide cyber security legislation designed to improve the security and resilience of critical services across EU member states.
The NIS Directive was published by the EU Commission on May 10th 2018 to address the growing volume and scale of cyber threats, and introduces several key requirements for Operators of Essential Services (OES) and Relevant Digital Service Providers (RDSPs) within the EU, including:
- Taking appropriate measures to manage the risks to critical technologies.
- Taking appropriate measures to prevent incidents and reduce the impact of incidents when they occur.
- Paying attention to what relevant Competent Authorities ask of them.
- Notifying their Competent Authority if they identify incidents which have negative impacts on their ability to deliver their essential services.
What are the NIS Regulations?
The NIS Regulations are the UK’s implementation of the NIS directive; they are domestic UK law. Put simply, if you work for an OES in the UK, the NIS Regulations are usually where you should be focused. (If you aren’t sure whether you’re an OES, see the ‘Who Must Comply with the NIS Regulations?’ below.)
See our recent webinar for more on changes to the NIS regulations and NIS 2.
What is the Difference between the NIS Directive and the NIS Regulations?
The NIS Directive originated at the EU level and required that Member States introduce their own national legislation to protect critical network and information system. The NIS Regulations are the UK’s national legislation to implement the NIS Directive.
While the NIS Directive provided some high-level steer on how national legislation should be written, the Directive also allowed a lot of flexibility. Member States – such as the UK – were allowed to determine which organisations should be considered OES or RDSPs, and what actions were ‘appropriate and proportionate’ to manage the risks associated with IT and OT systems.
Who Must Comply with the NIS Regulations?
The NIS regulations apply to:
Operators of Essential Services (OES):
- Energy (electricity, oil and gas)
- Transport (aviation, rail, maritime and road)
- Health (including hospitals, private clinics and online settings)
- Drinking water (supply and distribution)
- Digital infrastructure (TLD name registries, DNS resolver services / authoritative hosting services, Internet Exchange Points)
Relevant Digital Service Providers (RDSPs)
- Providers of online marketplaces
- Providers of online search engines
- Providers of cloud computing services

Whether or not a specific organisation is in scope of the NIS Regulations depends on a range of factors which are beyond the scope of this guide. Some critical sectors – notably finance and civil nuclear – are also exempt from the NIS Regulations on the basis that they are subject to equivalent security and resilience requirements under other legislation.
The NIS Regulations also designate Competent Authorities for each of these sectors – typically either government/ devolved ministers, sector regulators, or a mix of both.
What Are the NIS Regulation’s Requirements for OES and RDSPs?
The NIS Regulations introduce four obligations which OES and RDSPs must meet:
- Take measures to manage the risks to critical technologies
- Take measures to prevent incidents, and reduce the impact of incidents when they occur
- Pay attention to what Competent Authorities ask of them
- Notify their Competent Authority if they identify incidents which have negative impacts on their ability to deliver their essential services
The NIS Regulations do not prescribe any specific technical controls or mandate compliance with particular standards or frameworks, such as ISO 27001 or the NIST Cyber Security Framework. Instead, they leave wide discretion for Competent Authorities to determine what is reasonable and proportionate.
This means that some Operators of Essential Services may be expected to meet higher or lower requirements depending on their sector. For example, OES that deliver a critical service to a larger number of customers, or provide a service which other Operators of Essential Services are critically dependent upon, will have more demanding requirements.
How Can Operators of Essential Services Achieve Compliance with the NIS Regulations?
To support OES and Competent Authorities in demonstrating their compliance with the NIS Regulations, the National Cyber Security Centre (NCSC) has developed 14 core security and resilience principles, together with a range of supporting material collectively known as the Cyber Assessment Framework (CAF). Most Competent Authorities have adopted the CAF, or variations of it, for sectors regulated under the NIS Regulations.
See this blog for more on what the CAF is and how it’s structured.
What are the NIS Incident Reporting Requirements?
Organisations subject to the NIS Regulations have clearly defined legal obligations to report incidents. For OES, this requirement extends to any incident that causes a ‘significant impact on the continuity of the essential service which that OES provides’, taking into account the number of customers and geographic area affected, and the duration of the incident.
Relevant DSPs are required to report any incident having a ‘substantial impact on any of the [relevant] digital services’ they provide, taking into account the number of users and geographical area affected, the extent of the disruption, the impact on social and economic activities, and the duration of the incident.
Precise reporting processes vary by sector and are defined by the individual competent authorities.
What Are the Consequences for Non-compliance With the NIS Regulations?
If Competent Authorities identify breaches of the Regulations, they can issue enforcement notices requiring specific or general improvements and are also empowered to issue fines of up to £17,000,000 for egregious breaches.
In some instances, an OES or DSP could face liability under both the NIS Regulations and the GDPR Regulations for the same incident. The government has stated that OES and DSPs should not ordinarily be fined under both Regulations, unless the dual penalties “relate to different aspects of wrongdoing and different impacts”.
What is NIS2?
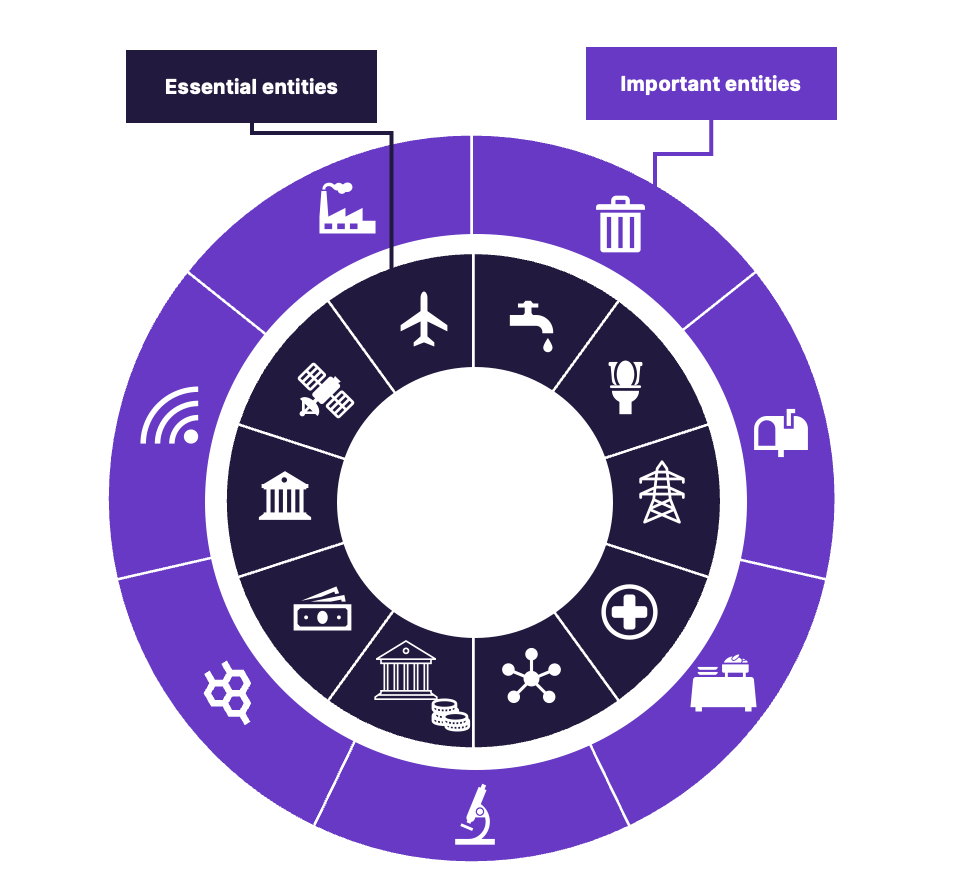
NIS2 significantly expands the range of in-scope sectors and organisations compared to the original set of regulations. It replaces the distinction between ‘Operators of Essential Services’ and ‘Digital Service Providers’ with two new categories:
- 'Essential Entities’: these are broadly the typical Critical National Infrastructure sectors that were originally defined as OES in NIS1.
- ‘Important Entities’: other large and medium-sized organisations which play an important role in the economy. This includes post and courier services, waste management, chemicals and research. Important Entities are subject to lower levels of oversight than Essential Entities.
The NIS2 Directive also introduces direct obligations on the ‘management bodies’ of Essential and Important Entities; includes more explicit compliance requirements; and strengthens reporting obligations compared to the original NIS1 Directive.
EU Member States must ‘transpose’ (i.e. bring their domestic law into alignment with) the NIS2 Directive by 17 October 2024.
Brexit and the NIS Regulations
The NIS Regulations continue to apply after Brexit. However, the UK Government has decided that the NIS2 Directive will not apply in the UK.
“Given that the UK is no longer bound by EU legislation and will not be implementing NIS 2.0 there will be differences between the EU and the UK. The UK’s legislation is designed for the UK economy and to maximise the benefits to the UK.” (Proposal for legislation to improve the UK’s cyber resilience – Government response, 30 November 2022)
The UK Government has instead published its own proposals to enhance the NIS Regulations. These include extending the NIS Regulations to cover Managed Service Providers, reflecting the critical role they can play in overall security and resilience, and expanding the range of incidents which must be notified to Competent Authorities. Although these changes are more modest than those contained in the NIS2 Directive they will require changes to legislation, and it is not currently clear when they will be introduced.

.jpg?sfvrsn=680254a0_1)