Tycoon2FA Infrastructure
To recover from this recent takedown, the actors behind Tycoon2FA didn't waste any time worrying about their 330 seized domains. Instead, they quickly recovered from this and within a few weeks they were back hosting new domains.
Recent analysis confirms that there was a dip in Tycoon2FA domains after the takedown but we can see that this didn't last for long and the numbers are already rising as shown in Figure 1.
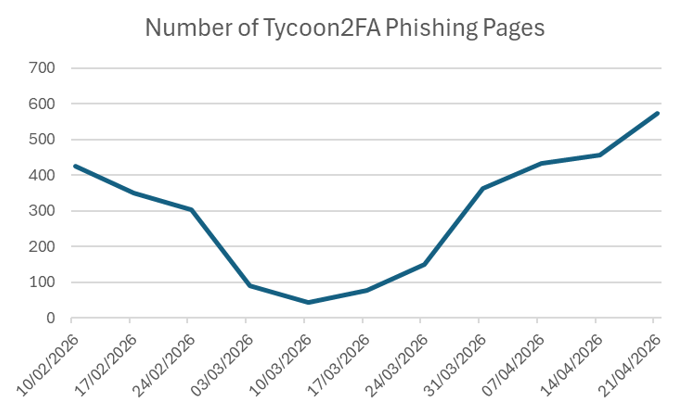
Figure 1 - Timeline showing identified Tycoon2FA infrastructure over time
A review of the urls show that the threat actor has shifted their focus from the previously reported url patterns and appear to be using new methods.
Massive Abuse of Legitimate Cloud Infrastructure
· To bypass reputation-based email security gateways, the operators heavily abuse legitimate cloud hosting and Content Delivery Networks (CDNs) rather than solely relying on their own registered domains
o CloudFlare:
he attackers extensively utilize Cloudflare Workers (*.workers.dev) and
Cloudflare Pages (*.pages.dev) to host their dynamic phishing payloads and
proxy relays
· The URLs provide direct evidence of Tycoon 2FA's Adversary-in-the-Middle (AiTM) capabilities. Dozens of URLs contain long query strings resulting in the Microsoft error AADSTS50058
o This specific Microsoft Entra ID (Azure AD) error indicates that "A silent sign-in request was sent but no user is signed in"
Subdomain Mimicry and Thematic Lures
· Aligning with known Tycoon 2FA social engineering tactics, the attackers create highly specific subdomains that match the content of their phishing emails to lower victim suspicion
o Missed Voicemail / Audio Lures: A massive cluster of Cloudflare Workers is dedicated entirely to fake audio messages.
o Document and E-Signature Mimicry: The infrastructure heavily mimics secure file sharing and e-signature platforms to steal Microsoft 365 or Google Workspace credentials.
Data Comparison
If we compare this to the previous dataset we originally tracked before the takedown of their infrastructure, there is some overlaps in the new infrastrucutre.
Subdomain Impersonation
Analysis confirms the continued use of tech and document-themed subdomains, but shows a massive pivot toward abusing legitimate cloud hosting providers and a new thematic focus.
· Instead of solely relying on registered domains, the attackers are now heavily abusing trusted SaaS platforms to host their payloads.
Path and Suffix Structure
The mechanics of how Tycoon2FA tracks victims and structures its URL paths remain incredibly consistent
· The Alphanumeric Hash: The use of seemingly random hashes interspersed with ! and @ is perfectly preserved. The new dataset shows hundreds of examples utilizing this exact syntax, such as /POEt!v04XFJWYFVlPxkAQGyOs/, /54yO!4iBQ1LQPHUelGCjFOflR/, and /Je!28Kgv/.
· Victim Identification Suffix (/$ and /*): This remains the primary method for tracking targets and pre-filling fake login pages. The dataset shows heavy use of the /$ prefix (e.g., /$jared@squaredeal.com, /$victorm@invercap.com.mx) and the /* prefix (e.g., /*no.thanks@associatedbank.com).
· Encoded Emails: The use of Base64 encoded email addresses ending in = or == remains a staple evasion technique in the new data (e.g., /$bWljaGVsbGUuaXJvbnNAZ29ndWxmd2luZHMuY29t, /$YW5kcmVhLnB1bHZpcmVudGlAYWxpcmFoZWFsdGguY29t).
Domain and TLD Trends
The underlying strategy for procuring domain names remains unchanged, though some specific families have evolved.
· Suspicious TLDs: The reliance on cheap, disposable TLDs is identical. The new dataset is dominated by .ru (e.g., crojuyai.ru, dashithoo.ru), alongside frequent use of .biz.id, .sa.com, .digital, .my.id, and .team.
· Pseudo-Random Domain Names: The use of nonsensical, procedurally generated words remains the standard for their root domains
Strategic Outlook
The evolution in Tycoon 2FA's URL patterns highlights a fundamental shift in the defensive landscape. When attackers can seamlessly blend their credential-harvesting mechanisms and thematic lures (like missed voicemails) into the exact same SaaS platforms and CDNs that legitimate enterprises rely on, reactive domain blocklisting becomes entirely obsolete. You cannot blindly block *.workers.dev or Azure subdomains without actively breaking your own business operations.
Furthermore, the persistent footprint of Adversary-in-the-Middle (AiTM) tactics—evidenced by the continuous generation of AADSTS50058 Microsoft authentication errors in their proxy URLs—proves that their core objective remains unchanged. Despite the infrastructure rotation, their underlying mechanics for tracking victims and bypassing standard Multi-Factor Authentication (MFA) are still fully operational.
Defenders must accept that the PhaaS ecosystem is highly resilient; if a core network is seized, operators will procedurally generate new burner domains on cheap TLDs like .ru or .biz.id within days. To survive this post-takedown landscape, security teams must shift their focus from the perimeter to the identity layer.
Defeating the zombie infrastructure of Tycoon 2FA requires rendering their AiTM attacks useless. This demands a complete transition to phishing-resistant authentication (such as FIDO2 security keys or passkeys) and continuous Identity Security Posture Management (ISPM) that monitors for anomalous session token behavior, rather than just relying on legacy login checks.





