Key Takeaways
- Subsea cables are now considered critical infrastructure, not just commercial telecoms assets.
- State-linked activity has increased concern around physical sabotage and hybrid warfare.
- New US, EU and UK regulatory frameworks are creating more complex compliance requirements.
- Cable system operators need stronger governance, supply chain assurance, physical security and cybersecurity risk management.
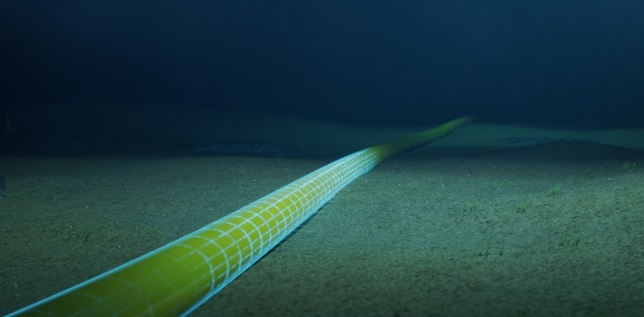
Subsea cable security has become a critical concern for governments, telecoms operators and cloud providers. More than 99% of international data traffic travels through subsea fibre-optic cable systems, carrying internet traffic, financial transactions, military communications and the data that powers artificial intelligence. Once treated largely as commercial infrastructure, submarine cable systems are now recognised as critical global infrastructure and a growing target for cyber, physical and geopolitical threats.
However, over the last few years, the geopolitical landscape has shifted, and these subsea cable systems are no longer deemed a commercial asset, but part of critical global infrastructure, as strategically important as power grid networks. As a result, greater regulatory change is being driven across the US, EU and the UK.
Why Subsea Cable Infrastructure Is Now a Critical Security Risk
The key shift in the threat landscape has been the direct willingness of state actors to physically attack subsea infrastructure. In November 2024, two telecommunication cables were disrupted in the Baltic Sea within 24 hours of each other; in the months that followed, a further five cables were cut in the region, with investigations pointing to vessels with suspected links to Russian intelligence operations.
In April of this year, the UK Defence Secretary stated that a British warship had to be deployed to deter three Russian submarines, operating in the Atlantic, from conducting cover operations, which could cause damage to UK infrastructure.
More recently, the Chinese have announced that they have been testing a new device capable of slicing through cables thousands of metres deep beneath the surface - increasing concerns of such equipment being used for sabotage.
The pattern is clear: subsea cables are no longer only vulnerable to accidental damage from fishing trawlers and ship anchors. They are increasingly being treated as instruments of hybrid warfare, making maritime cyber threats and physical resilience a board-level risk for cable system operators.
There is an explosive growth in demand for bandwidth, being driven by cloud computing, streaming and the increased use of AI technology. This has led to a massive concentration of global internet traffic across a number of very high-capacity cable system; many of which are owned or co-owned by a handful of hyperscalers. This concentration creates a small set of extremely high-value targets - no longer disrupting a fraction of a country’s internet, but taking down significant portions of a continents cloud infrastructure.
The Regulatory Landscape for Subsea Cable Security
In December 2024, the US regulatory body, the FCC, issued a Notice of Proposed Rulemaking (NPRM) signalling its intent to modernise the existing rules of cable landing licensing. By August 2025, it adopted a comprehensive Report and Order program, which set out to overhaul US subsea cable regulation, expanding the scope of cable system compliance to include not only Service Line Terminal Equipment (SLTE) hosted in landing stations, but also relevant inland infrastructure such as data centres.
In addition, this order introduced greater rules in declaring foreign ownership in a co-owned cable systems, mandatory cybersecurity and physical security management plans - ensuring all aspects of a cable system, including third-party contractors and supply chain partners implemented appropriate security risk mitigation measures.
Europe’s regulatory response to the subsea cable threat has been equally ambitious. The EUs framework rests on four interlocking pillars: the NIS2 Directive, the Critical Entities Resilience (CER) Directive, the EU Action Plan on Cable Security, and the newly introduced Cable Security Toolbox.
The NIS2 Directive
The NIS2 Directive is the EU’s flagship cybersecurity legislation. It includes operators of Submarine Data Transmission Infrastructure (SDTI) as a sector of high criticality and covers not only the cables themselves, but also infrastructure essential to their operation, including cable landing stations and terrestrial portions of the network.
EU Cable Security Action Plan on Cable Security
In February 2025, the European Commission and the High Representative for Foreign Affairs and Security Policy adopted the EU Action Plan on Cable Security. This outlines a framework for preventing, responding to and recovering from threats to submarine cable infrastructure.
The Cable Security Toolbox
The EUs Submarine Cable Infrastructures Expert Group published the Cable Security Toolbox. This document represents the most detailed and actionable set of EU guidance for cable operators to date, covering Strategic Measures, Technical Support Measures and identifies thirteen prioritised areas for Cable Projects of European Interest (CPEIs).
UK Telecoms Security and Subsea Cable Resilience
As an island nation, the UK occupies a uniquely vulnerable position in the global cable network, where the country is almost entirely dependent on subsea cables for its international connectivity. A dedicated inquiry was launched in February 2025 by the UK Parliament’s Joint Committee on the National Security Strategy, which published its findings the following September.
The UK’S primary legislative framework for telecoms security is the Telecommunications Act 2021 (TSA). Ofcom, as the UKs communications regulator, is responsible for enforcing the TSA, and they actively work with their international partners - including in the US, EU and Five Eyes alliance countries - to develop a coordinated cable security approach.
What Compliance Means for Cable System Operators
The convergence of these regulatory frameworks creates a complex, multi-jurisdictional compliance challenge for cable system operators and their sub-contractors, specifically with cables landing in more than one country, and various continents.
To counter this, a practical approach to compliance is required. Bridewell, in collaboration with a hyperscaler who operate as a cable system operator, have developed a framework for subsea cable system compliance, which covers the full-lifecycle of a cable system (design-procure-build-deploy-operate-decommission). The framework includes the following guidance:
Map Your Regulatory Exposure: Understand which regulatory regimes apply to your operations, including FCC, NIS2, CER, EU cable security guidance and UK telecoms security requirements.
Implement a Comprehensive Supply Chain Audit: regulators require detailed and up-to-date information of every piece of equipment within the cable system infrastructure, details on all vendors, suppliers, sub-contractors, manufacturers, distributors, service providers, etc. In addition, details on individuals who have been fully screened and have unescorted access to cable systems (logical and physical access) may also be required to be provided to regulatory bodies during annual filings.
Develop and Document Your Cyber Security Risk Management Plan: System operators and their vendors should ensure that formal cyber security risk management plans are implemented, documented, reviewed and updated. These plans should cover all aspects of the cable system lifecycle. Bridewell has designed a cable system security and compliance control framework that aligns with standards such as ISO 27001 and NIST, while focusing on the detailed requirements of the full cable system lifecycle.
Harden Your Physical Infrastructure: the EUs Cable Security Toolbox and the UK Parliamentary Committee’s recommendations emphasise the importance of physical security at cable landing stations. Operators should therefore implement a comprehensive audit program that includes all vendors and facilities - such as cable landing stations and network operating centres - testing both physical security and cybersecurity compliance in line with security risk management plans.
Prepare for Enhanced Scrutiny of Ownership and Transactions: The FCC, under their new rules, require that any change in ownership (in the UK and US), or any significant change in the management of a cable system will face enhanced scrutiny. Operators should build regulatory review timelines into their transaction planning to ensure that ownership structures are transparent and well-documented.
Engage with Regulators Proactively: Don’t wait for the regulators to come knocking at your door. Operators who engage proactively - providing technical expertise, flag unintended consequences and demonstrate their commitment to security - will be better positioned to influence the rules and build regulatory relationships.
The ocean floor has changed. The subsea cable industry has always operated at the intersection of technology, commerce and geopolitics. What has changed is the intensity of the geopolitical dimension. This is now a contested space, and the infrastructure that lies beneath it is a strategic asset that governments are determined to protect and control.
The regulatory frameworks described in this article are not the end of the story, they are the beginning of a new chapter in which security and compliance will be fundamental to the cable industry… the tides have turned. Are you ready to navigate the new currents?
Frequently Asked Questions
What are the main cyber threats to subsea cables?
The main risks include physical sabotage, attacks on cable landing stations, compromise of network management systems, supply chain weaknesses, insider threats and disruption linked to hybrid warfare.
Why are subsea cables considered critical infrastructure?
They carry international internet traffic, financial data, military communications and cloud connectivity, making them essential to economic resilience and national security.
How does NIS2 affect subsea cable operators?
NIS2 brings submarine data transmission infrastructure into a high-criticality category, increasing expectations around governance, risk management, incident reporting and supply chain security.
What is the EU Cable Security Toolbox?
The Cable Security Toolbox provides practical measures to improve the prevention, detection, response and recovery capabilities of submarine cable infrastructure across Europe.
What should cable system operators do to improve compliance?
Operators should map regulatory exposure, audit supply chains, document cybersecurity risk management plans, harden landing stations and network operating centres, and engage proactively with regulators.